FBI says Iranian hackers are using Telegram to steal data in malware attacks
According to officials, these cybercriminal groups are leveraging Telegram as a **command-and-control (C2) channel**, allowing them to manage attacks remotely while staying difficult to trace.

The FBI has issued a warning that Iranian-linked hackers are increasingly using the messaging platform Telegram to coordinate malware attacks and steal sensitive data.
According to officials, these cybercriminal groups are leveraging Telegram as a command-and-control (C2) channel, allowing them to manage attacks remotely while staying difficult to trace.
The alert highlights a growing trend in cyber warfare where attackers are using popular communication platforms to hide malicious activity, making detection and prevention more challenging.
How Hackers Are Using Telegram
Cybersecurity experts say attackers are using Telegram in multiple ways to execute their operations.
These include:
- Sending commands to infected devices
- Exfiltrating stolen data
- Managing malware campaigns remotely
- Communicating securely within hacking groups
Because Telegram offers encryption and bot-based automation, it has become an attractive tool for cybercriminals.
This allows attackers to operate covertly while maintaining real-time control over compromised systems.
What Kind of Malware Is Being Used
The FBI warning suggests that hackers are deploying different types of malware designed to infiltrate and exploit systems.
Common malware capabilities include:
- Stealing login credentials
- Capturing sensitive files
- Monitoring user activity
- Installing additional malicious software
Once a system is infected, the malware connects back to Telegram channels or bots, allowing attackers to control devices and extract data remotely.
Why Telegram Is Being Exploited
Telegram’s features make it useful not just for communication—but also for misuse.
Key reasons include:
- Encrypted messaging capabilities
- Bot creation for automation
- Easy file sharing
- Cross-platform accessibility
While these features are designed for privacy and convenience, attackers exploit them to coordinate cyberattacks and hide their activities.
Who Is at Risk
The attacks are not limited to a specific group of victims.
Potential targets include:
- Businesses and enterprises
- Government organizations
- Remote workers
- Individual users
Anyone who interacts with suspicious files or links could unknowingly become a victim of malware infection.
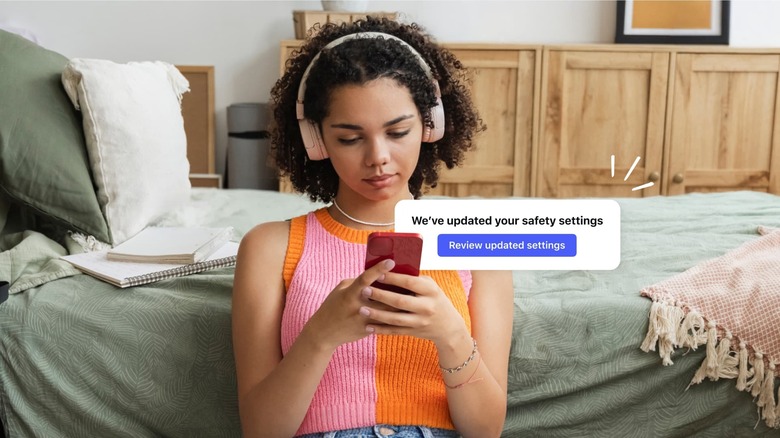
How to Protect Yourself from These Attacks
To stay safe, experts recommend taking proactive cybersecurity measures:
- Avoid clicking unknown links or downloading suspicious files
- Use strong and unique passwords
- Enable two-factor authentication
- Keep your software and devices updated
- Install reliable security tools
Awareness and caution are critical in preventing data theft and malware infections.
The Bigger Picture: Evolving Cyber Threats
This warning reflects a broader shift in cyber threats.
Modern attacks are becoming:
- More sophisticated
- Harder to detect
- Increasingly state-linked
- Dependent on everyday apps
Cybercriminals are adapting quickly, using widely available tools to blend in with normal user activity.
Final Thoughts
The FBI’s alert about hackers using Telegram highlights how cyber threats are evolving with technology.
As attackers continue to exploit common platforms, individuals and organizations must stay vigilant and informed.
By understanding these risks and adopting strong security practices, users can significantly reduce their chances of becoming victims.
In today’s digital world, staying secure online is more important than ever.
FAQ
What did the FBI warn about?
The FBI warned that Iranian-linked hackers are using Telegram to coordinate malware attacks and steal data.
How are hackers using Telegram?
They use it as a command-and-control system to manage infected devices and extract data.
What kind of malware is involved?
Malware that can steal credentials, monitor activity, and install additional threats.
Why is Telegram being targeted?
Its encryption, automation features, and global accessibility make it useful for attackers.
Who is at risk?
Businesses, government agencies, and everyday users can all be targeted.
How can I protect myself?
Avoid suspicious links, update your software, and use strong security practices.
Mentioned in this article
Tools

Kick
Kick is an innovative AI-powered bookkeeping software designed to automate financial management f

Kick is an innovative AI-powered bookkeeping software designed to automate financial management for businesses and individuals, offering a “self-driving” approach to accounting. It addresses the common challenges of manual bookkeeping – time consumption, potential for errors, and the need for spe

NoteDock
NoteDock is an intelligent AI-powered note-taking and task management platform designed to help u

NoteDock is an intelligent AI-powered note-taking and task management platform designed to help users capture, organize, and recall information with unprecedented efficiency. It addresses the common problem of information overload and the difficulty of retrieving crucial details from scattered

DreamStories
DreamStories is an innovative AI-powered bedtime story generator that creates personalized narrat

DreamStories is an innovative AI-powered bedtime story generator that creates personalized narratives for children, transforming bedtime into a magical and engaging experience. DreamStories addresses the challenge of consistently providing fresh, captivating content for children’s bedtime routine

Amino: Supplement Scanner
Amino: Supplement Scanner is an AI-powered supplement analysis application designed to help users

Amino: Supplement Scanner is an AI-powered supplement analysis application designed to help users make informed decisions about dietary supplements by leveraging artificial intelligence, a comprehensive database, and advanced analytics . This tool addresses the growing concern of supplement sa

Kilo | Cloud Agents
Opening Overview Kilo | Cloud Agents is a powerful AI-powered cloud development platform designed

Opening Overview Kilo | Cloud Agents is a powerful AI-powered cloud development platform designed to help developers streamline the entire software creation process by leveraging artificial intelligence, automation, and intelligent cloud-based workflows . By shifting the development environmen
Vivgrid
Vivgrid is an AI agent platform that empowers developers and organizations to build, evaluate, and

Vivgrid is an AI agent platform that empowers developers and organizations to build, evaluate, and deploy artificial intelligence agents with confidence. It addresses the critical need for robust testing and monitoring in the AI agent lifecycle, ensuring reliability and performance. This platform i

OfferScope
OfferScope is an AI-powered employment contract analysis tool designed to help users understand

OfferScope is an AI-powered employment contract analysis tool designed to help users understand the terms of their job offers by leveraging artificial intelligence and natural language processing . OfferScope addresses the critical problem of employment contract complexity, where individuals o

Learn Place Verified Experience
Learn Place Verified Experience offers an innovative AI-Powered Online Internship Program for studen

Learn Place Verified Experience offers an innovative AI-Powered Online Internship Program for students and graduates, providing invaluable AI-Verified Experience. This platform revolutionizes traditional internships by offering virtual, project-based learning opportunities enhanced by artificial int

Nexi - AI Co‑Host for Twitch & YouTube Streamers
Nexi is an innovative AI Co-Host specifically designed for Twitch and YouTube streamers, acting as a

Nexi is an innovative AI Co-Host specifically designed for Twitch and YouTube streamers, acting as an intelligent stream companion that actively entertains chat and boosts tips. This AI-powered widget integrates seamlessly with popular streaming platforms like StreamElements, providing real-time, dy

PhonePi MCP
PhonePi MCP is an innovative AI automation platform that empowers users to connect their smartpho

PhonePi MCP is an innovative AI automation platform that empowers users to connect their smartphones directly to artificial intelligence models, enabling context-aware automation and enhanced mobile productivity. PhonePi MCP addresses the challenge of fragmented digital workflows by providing a u